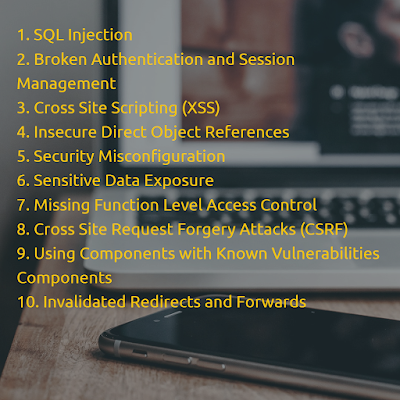
Web application security risk is explained in OWASP. This is worldwide community for security which explained about security risk to people or organizations. Full name of OWASP is, The Open Web Application Security Project. OWASP have define different types of vulnerabilities through which unauthorized user can access data of protected site or application. OWASP have aim of speeding concerns about the security of the application. Below are the details of each vulnerabilities.
- SQL Injection: This technique is very common. When data base input and other parts of web application is not synchronized well at that time unauthorized user can attack on same portion of application and get inside to harm the data. SQL injection simply pass with SQL queries or commands. The thought behind injection is, it makes system ignoramus and tried to get inside.
- Broken Authentication and Session Management: When functions authentication workflow is not developed properly at that time unauthorized person can go through the protected information. If this will happen in any application then it allows unauthorized person to exploit users password, personal information , protected data, session keys etc. Also he can do inaccurate implementation via valid credentials of any user.
- Cross Site Scripting (XSS): When application accepts data from unauthorized user and accepts it as credentials this can call cross site scripting. Here wrong people can give credentials and it is not validated by web browser. Thus, monitor and control functions are not performed properly which allows attacker to damage web site by applying harmful code. A successful attacker can manage session too. Thus, by commanding on original website, attacker can transfer valid user to another websites.
- Insecure Direct Object References: In this vulnerability, unauthorized user can modify the internal code and implementation of object in terms of access control of an application. Internal changes can be done in database, URL and files. Attacker manipulate the internal data of an application here if authentication is not done properly. To prevent this, Developer can use indirect reference map as direct reference map can be easily known by attackers.
- Security Misconfiguration: While building any web sites or application, if security implementation is not building strongly then attacker can do unauthorized things with weak point of application. With use of security misconfiguration, they will first try to get inside with weak implementation and afterward they can access privilege data too. To restrict this, Configuration of application must be done properly. Not a single loop holes can be found by attackers. Perfect server and environment should be used to run the application.
- Sensitive Data Exposure: Sensitive data exposure can be implemented when SSL and HTTPS security controls are not properly developed for any website or application. Here data can be stolen and leaked with sensitive data exposure. If personal information is not secured properly then it will be a big risk. Security must be maintain for encrypted and protected data at transport layer. If developer team is fail to configure this in application then there are many weak points in website and application it provide access to expired privacy.
- Missing Function Level Access Control: When application have so many ways to gives rights to user and wrong writes have been provided to wrong person then he can easily get inside the application. As all functionality have been verified as per rights, unauthorized person can access all data as per given rights. Thus, Permission of rights must be taken seriously for this kind of application.
- Cross Site Request Forgery Attacks (CSRF): Here cookies and authentication can be managed by an unauthorized person so correct person will forget the HTTPS request. The web browser control have been taken by wrong person. Thus, all passed request have been verified by attacker.
- Using Components with Known Vulnerabilities Components: Sometimes we have idea about the known vulnerabilities in existing code, liberties and frame work which have been delivered from open source. This kind of already developed web sites and application can be first priority of attackers as they can easily apply SQL injection and XSS. We can prevent this by maintaining code in very proper manner and changing libraries and files as per convenient time period.
- Invalidated Redirects and Forwards: In most of the website, use have been redirected to other web page to access the data but if those pages does not have valid credentials then user may redirect on phishing or malware sites and this way unknowingly they will access the wrong page. To prevent this it’s better to not use backward and forward redirection in application and if it is necessary then user details must not be redirected to the destination page.
No comments:
Post a Comment